Updates
I have been selected to participate in the 13th Heidelberg Laureate Forum (HLF), held from September 13 to 18, 2026. It is a great opportunity to meet and exchange ideas with the laureates of the most prestigious awards in mathematics and computer science — the Abel Prize, the ACM A.M. Turing Award, the ACM Prize in Computing, the Fields Medal, the IMU Abacus Medal, and the Nevanlinna Prize — alongside fellow young researchers from around the world.
We have two papers accepted at NSDI 2026! The first paper, Eywa, led by students Rajdeep Mondal and Rathin Singha, uses LLMs to automatically build rich models of protocol behavior from RFCs and other natural language sources for model-based testing, discovering 33 unique bugs across DNS, BGP, and SMTP implementations. The second paper, MetaEase, led by student Pantea Karimi, introduces a practical analyzer that identifies worst-case heuristic performance directly from source code, eliminating the need for formal modeling.
Concord, a data-driven system that automatically learns lightweight network contracts for scalable configuration validation will appear at EUROSYS 2026.
Our work, led by Behnaz Arzani, that can analyze probable degradation of traffic engineered networks under arbitrary failures and traffic shifts would appear at SIGCOMM 2025.
We have two exciting papers accepted at HotNets 2024! The first paper, led by our student Pooria Namyar, explores the performance analysis of learning-enabled systems, for example, DNNs in cloud systems. The second paper, led by students Pantea Karimi and Solal Pirelli introduces $\mathcal{X}$plain, a tool that helps operators understand when and why their heuristics underperform.
Ryan and I co-presented our paper, Diffy: Data-driven Bug Finding for Configurations at PLDI 2024.
Our work on rethinking machine learning collective communication as a multi-commodity flow problem would appear at SIGCOMM 2024.
Our work on development of a push-button configuration analyzer, Diffy, that detects likely bugs in structured configurations, with Francis Y. Yan and Ryan Beckett, would appear at PLDI 2024.
I am serving again on the ANRW (Applied Networking Research Workshop) program committee!
I got invited to join the program committee for the ACM CoNEXT 2024 conference.
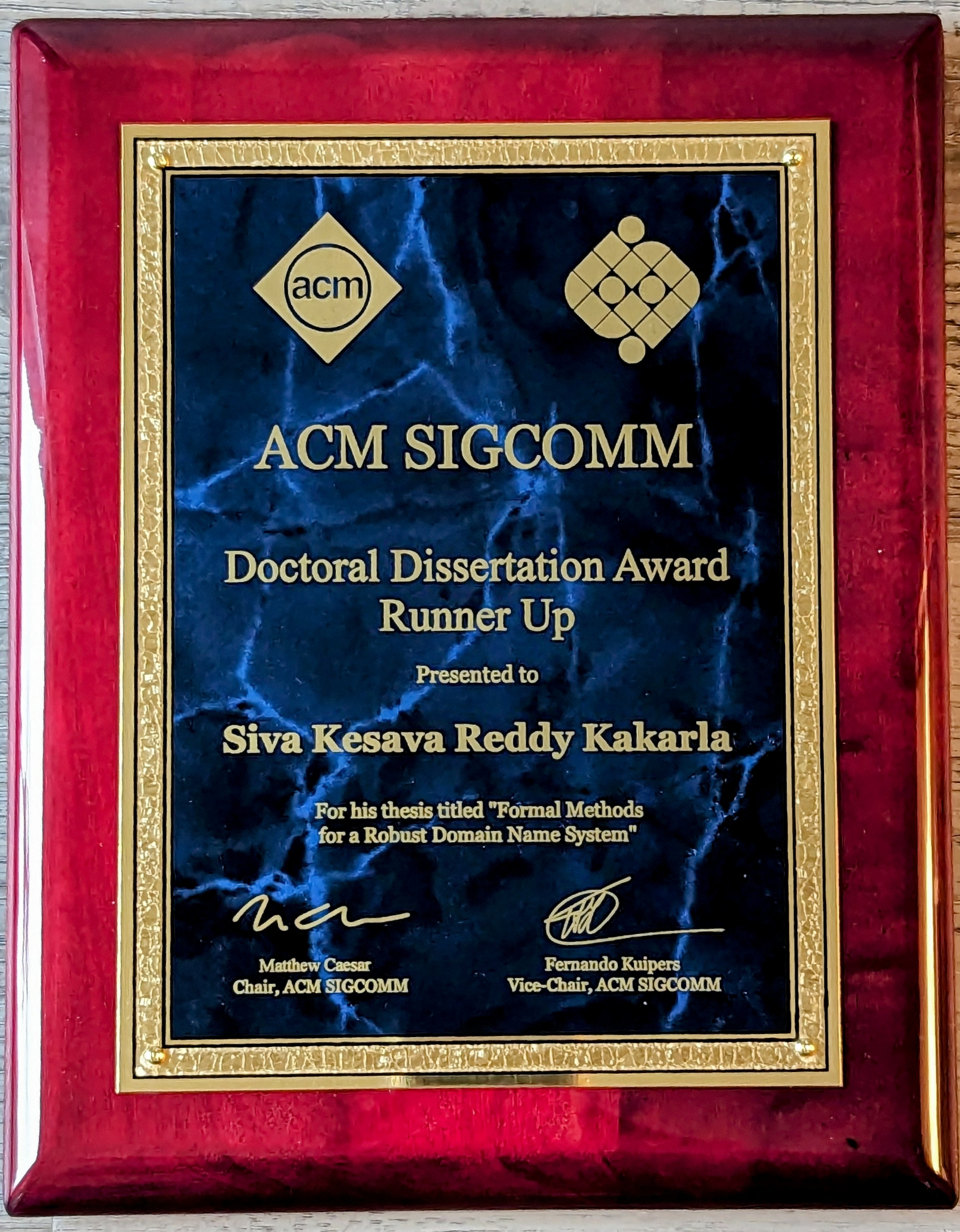
My thesis, “Formal Methods for a Robust Domain Name System,’’ won the runner up of the SIGCOMM Doctoral Dissertation Award for Outstanding PhD Thesis in Computer Networking and Data Communication. From the thesis award committee - “Found the research
impressively rigorous and thorough, and of critical importance to Internet security.”
In the initial round, I evaluated the posters and demos presented during the SIGCOMM 2023 poster and demo session. Subsequently, in the final round, I assessed the oral presentations delivered by the six finalists selected from the first round.
Led by Pouya, Behnaz, and Sadjad, our position paper exploring the use of Large Language Models (LLMs) in network incident management and considerations for designing an AI co-pilot has been accepted at HotNets 2023.
I am serving on the SIGCOMM 2023 Poster/Demo program committee. Looking forward to checking out some ongoing cutting edge research in networking.
I am serving on the IRTF 2023 Applied Networking Research Workshop program committee.
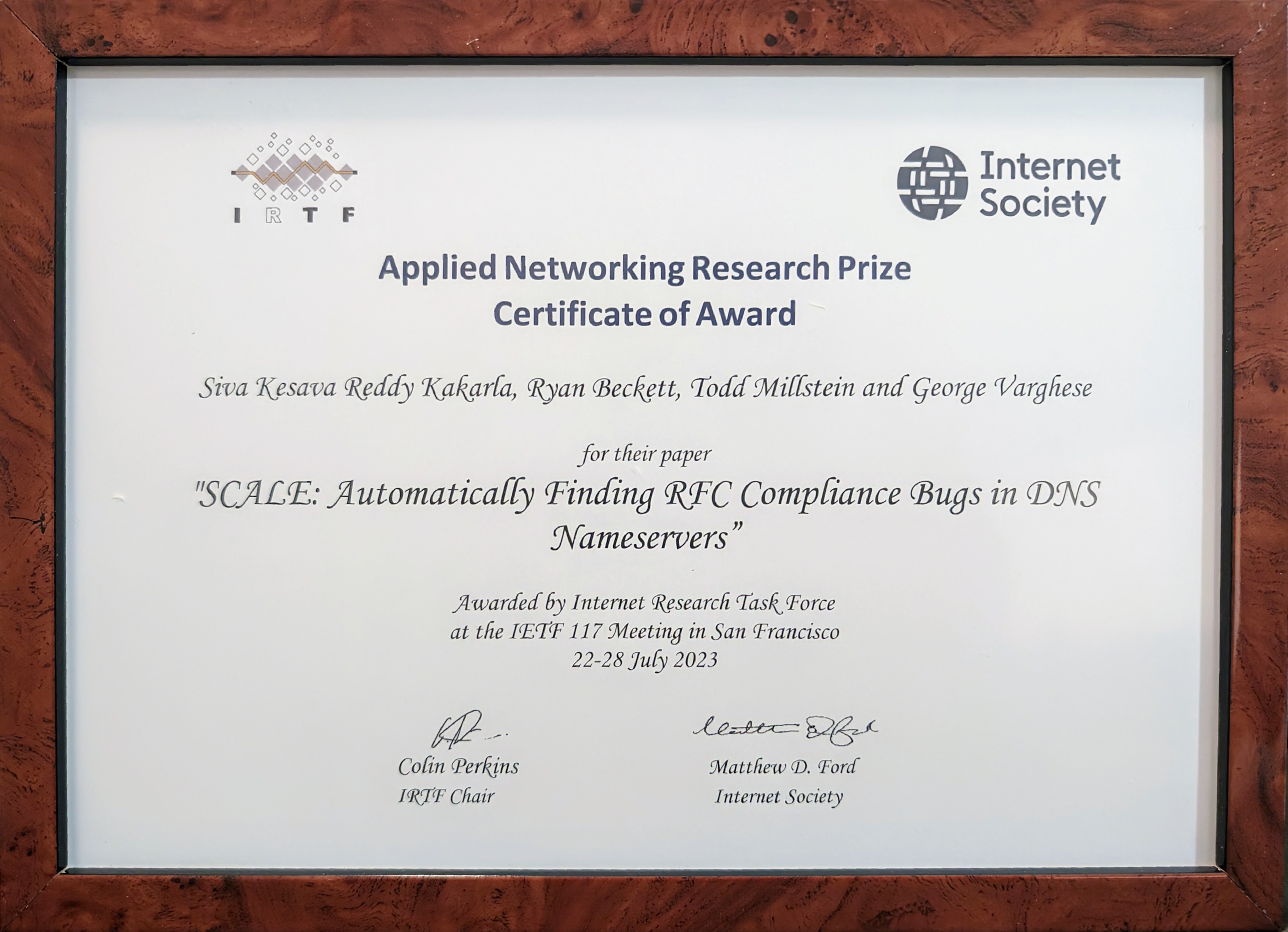
My NSDI ' 22 SCALE paper won the 2023 IRTF/IETF Applied Networking Research Prize (ANRP) award.
Mentions:
IETF Blog — Six Applied Networking Research Prizes Awarded for 2023,
IRTF Tweet — Six researchers have been announced as new #ANRP awardees this year for recent results in applied networking research and interesting new research of potential relevance to the Internet standards community.
In UCLA news: Computer Science
Other mentions: MSR tweet, Ranveer Chandra’s tweet, LinkedIn
I wrote an article titled ‘Harnessing Formal Methods Beyond Routing Layer,’ talking about some of my Ph.D. work, lessons I learned, and using formal methods beyond the network layer for the netverify.fun site.
I joined Ranveer Chandra’s networking research group at Microsoft Research, Redmond.
APNIC blog published a post titled, ‘Ferret: Automatically finding RFC compliance bugs in DNS nameservers’ based on our NSDI ' 22 paper.
Mentions:
APNIC Tweet — New #opensource tool ferrets out bugs in DNS nameservers, including
@bind9 @KnotDNS NSD & @powerdns,
APNIC Tweet — Ferret: Automatically find RFC compliance bugs in #DNS nameservers.
I am honored to be one of the four graduating doctoral students in CS
who received a Special Recognition in Research award from the engineering school (HSSEAS) at UCLA.
I am serving for the second time on the artifact evaluation committee of the SIGCOMM conference.
Deadlines: 2nd February (papers) · 11th June (artifacts)
I recorded an episode for the Hedge podcast discussing the DNS complexity from our HotNets paper.
I successfully defended my thesis (hybrid) - reached the final milestone of my PhD journey
It was an honor to have Ryan Beckett, Ravi Netravali, Yuval Tamir,
and my advisors Todd Millstein, and George Varghese on my committee!!
Slides: Formal Methods for a Robust Domain Name System

APNIC blog published a post titled, ‘How complex is the DNS’ based on our HotNets paper.
Mentions:
APNIC Tweet — Using the power of the DNAME record type, a #hotnets21 study shows the #DNS can express regular languages and pushdown systems,
APNIC Tweet — [DYK] The #DNS can recognize regular languages and generate strings in a context-free language.
Ferret was among the small subset of papers that appeared at NSDI 2022 to be invited for an article in the USENIX ;login: magazine.
I presented GRoot to the DNS community through the talk, Find Bugs in your DNS Zone files Before Deployment with GRᴏᴏᴛ at DNS-OARC 37 workshop.
I presented my Ph.D. work on how I use formal methods to make the DNS as robust as possible.
My research on automatically finding RFC compliance bugs in DNS nameservers by symbolically executing the DNS formal model, with Ryan Beckett and my advisors Prof. Todd Millstein and Prof. George Varghese, would appear at NSDI 2022.
I presented our results on the power and complexity of DNS at HotNets 2021.
I presented our work, “Exploiting Formal Methods To make The Domain Name System More Robust” at Network Verficiation Workshop, happening in conjunction with the 29th IEEE ICNP 2021 conference.
Talk Proposal: Towards a Robust DNS
⋮
Sep21
I am an applied research intern at Amazon Web Services (AWS) with John Backes. I am applying techniques from my DNS research of automatic test case generation for DNS nameserver implementations to Amazon’s DNS web service, Route 53.
My first shot at a short position paper exploring the complexity of DNS, along with Ryan Beckett, Prof. Todd Millstein, and Prof. George Varghese, got accepted at HotNets 2021.
I am honored to be one of final-year doctoral students who received the Dissertation-Year fellowship (DYF) awarded by the UCLA Graduate Division.
I am serving on the artifact evaluation committee of the SIGCOMM 2021 conference.
Artifact evaluation ensures that the results claimed in research papers are efficiently and accurately reproducible, facilitating further research. This is only the second year since SIGCOMM started artifact evaluation, so consider submitting the supporting artifacts for your research papers.
Deadlines: 27th January (papers) · 25th May (artifacts)
I presented our ongoing work, “So you think your Nameservers are Correct?” : Finding Errors Automatically in Nameserver Implementations at DNS-OARC 35 workshop.
Mentions:
DNS-OARC Tweet — “Incredible reception from the audience on
@SivaKesavaRK presentation. The automation tool received great compliments from the DNS experts”
Tweet from one of the audience — “As usual for DNS-OARC, #OARC35 is packed with interesting, useful DNS stuff. This one sounded impossible before the talk.”
Our work on debugging router configuration differences, led by Alan Tang, with Ryan Beckett, Ennan Zhai, Matt Brown, Prof. Todd Millstein, Prof. Yuval Tamir, and Prof. George Varghese, would appear at SIGCOMM 2021.
Ferret found a test input that can crash Bind. We reported it confidentially to the Bind security team, which fixed it and released a public disclosure.
Mentions: CVE Tweet
I was a finalist (top 3.5%) of the Facebook PhD fellowship program.
APNIC blog published a post titled, ‘Find bugs in your DNS zone files before deployment’ based on GRoot.
Mentions:
APNIC Tweet — DNS engineers have a new #opensource Guardian to help them catch bugs and prevent DNS-related outages,
LinkedIn — Interesting open source software to proactively identify DNS zone file errors,
APNIC Tweet — Zone file errors are all over the #DNS. With billions of potential queries, how can you check before deployment?,
APNIC Tweet — Bugs are everywhere in #DNS zone files. GRoot roots them out.
I passed the OQE, and have now advanced to candidacy — one more milestone reached!
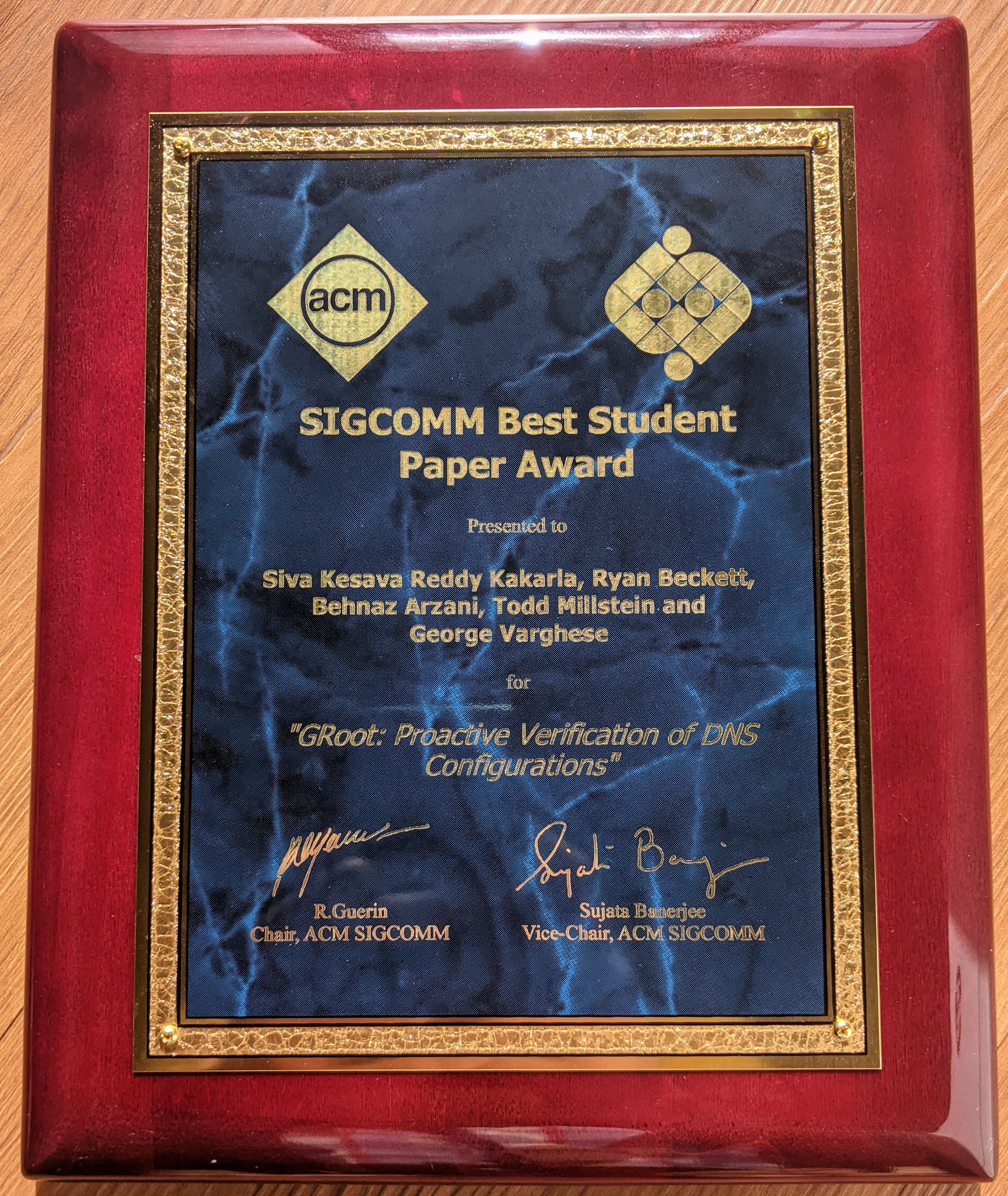
Our GRoot paper
received a best student paper award at SIGCOMM 2020.
This year $2$ out of the $53$ accepted ($250$ submitted) papers received this award.
In UCLA news: Computer Science
Other mentions: MSR tweet
I presented the GRoot work to the Intentionet team. (Invited by Ratul Mahajan)
⋮
Jun20
I am interning with Jayaram Mudigonda and Anees Shaikh from the NetInfra group. I am researching into config analysis techniques to uncover potential problems in Google’s metro-networks.
My research on proactive verification of DNS configurations, with Ryan Beckett and Behnaz Arzani and my advisors Prof. Todd Millstein and Prof. George Varghese, would appear at SIGCOMM 2020.
My work on finding network misconfigurations by automatic template inference with Ryan Beckett, Karthick Jayaraman, Prof. Yuval Tamir, and my advisors Prof. Todd Millstein and Prof. George Varghese, would appear at NSDI 2020 — yay! my first paper from PhD
⋮
Oct19
As a part-time remote applications developer, I am continuing my internship work to build GRoot, a DNS configuration verification tool with Ryan Beckett, and Behnaz Arzani.
⋮
Sep19
I am a teaching assistant for the upper-division Computer Network Fundamentals (CS 118) course, taught by my advisor Prof. George Varghese.
I presented my initial work on finding network misconfigurations by automatic template inference (SelfStarter) at Intentionet. (Invited by Ratul Mahajan)
I presented my first part of the internship work on DNS as a poster during the Microsoft Research Networking intern postern session event.
⋮
Jun19
I am interning with Ryan Beckett from the MNR group led by Victor Bahl. I am developing the first verification tool using static analysis for proactive and exhaustive checking of the DNS configurations (zone files) for common bugs. I am also working with Karthick Jayaraman on finding misconfigurations in Microsoft data center and WAN router configurations and aiming to submit the work to NSDI 2020 fall deadline.
I passed the WQE — one milestone reached on the journey to my PhD!
I am honored to be the one of the recipients of the Dean’s special fellowship for the 2018-2019 academic year.
I am honored to be the incoming PhD student to receive the prestigious GDSA fellowship by the UCLA Graduate Division.
I started my PhD journey at UCLA in the Computer Science department.

